Regulation (EU) 2024/2847 entered into force on December 10, 2024.
Most lighting manufacturers haven't read it but the ones who have are already moving. By December 11, 2027, every one of them selling networked products in Europe will need to comply with it.
The Cyber Resilience Act (CRA) establishes horizontal cybersecurity requirements for all "products with digital elements" sold in the EU market. That phrase covers any hardware or software with a direct or indirect data connection to a device or network. In practical terms for the entertainment lighting industry: if it has an Ethernet port, a Wi-Fi radio, or any network interface, it falls under the CRA.
Lighting consoles. DMX gateways. Network nodes. LED drivers with Art-Net inputs. Wireless DMX transmitters. Media servers. Architectural controllers with DALI or KNX interfaces. All of them.
The Timeline
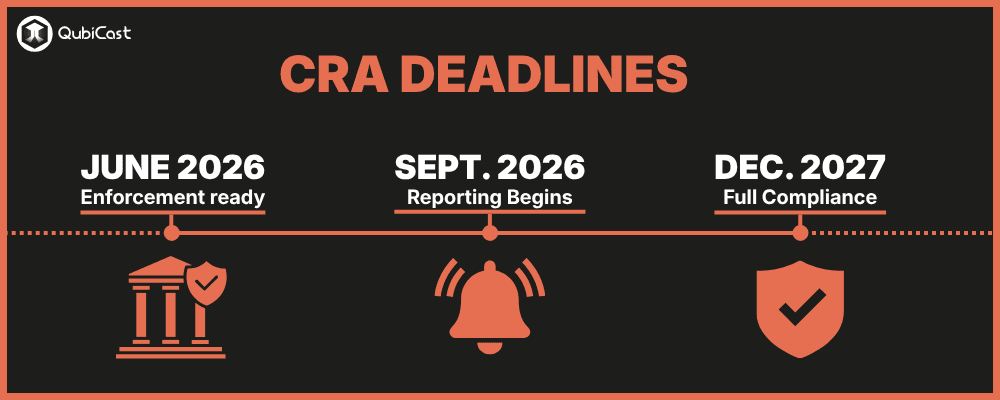
The CRA rolls out in three phases, and the first deadline is closer than most manufacturers realize.
June 11, 2026: Conformity assessment body notification procedures must be established. This is an administrative milestone for EU member states, but it signals that the enforcement infrastructure is being built.
September 11, 2026: Reporting obligations take effect. From this date, manufacturers must notify ENISA (the EU Agency for Cybersecurity) within 24 hours of identifying any actively exploited vulnerability in their products. This applies to all products already on the market, not just new ones.
December 11, 2027: Full application. Every networked product newly placed on the EU market after this date must meet all CRA requirements, including existing products that receive a substantial modification (such as a significant firmware or software update that changes functionality or intended use). Non-compliant products cannot carry the CE marking and cannot be legally sold in Europe.
That's roughly 19 months from now.
What "Compliance" Actually Requires
The CRA isn't a simple checkbox exercise. It requires manufacturers to integrate cybersecurity across the entire product lifecycle, from design through end-of-support. The core requirements fall into five areas.
Secure-by-design development. Products must be designed with cybersecurity in mind from the start. Manufacturers must conduct a risk assessment, identify threats relevant to their product's intended use, and implement appropriate protections before market release. The regulation uses the phrase "security by default," meaning products should ship in a secure configuration without requiring the user to take additional steps.
Conformity assessment. Manufacturers must perform technical evaluations to demonstrate compliance. The CRA defines four product categories (Default, Important Class I, Important Class II and Critical) with increasing assessment requirements. Most lighting products will likely fall under the "Normal" category, which allows self-assessment. Products classified as "Important Class II" or "Critical" require third-party assessment by a notified body. The European Commission published the technical descriptions of these categories in November 2025.
Vulnerability management. This is the requirement that will affect daily operations the most. Manufacturers must maintain a vulnerability handling process for the entire support period of their product, provide security updates for the full expected product lifetime, with five years as the minimum support period, and report actively exploited vulnerabilities to ENISA within 24 hours. That 24-hour clock starts when the manufacturer becomes aware of the exploitation, not when a patch is ready.
Technical documentation. Manufacturers must maintain documentation for at least 10 years, including a Software Bill of Materials (SBOM) listing all components, risk assessment reports, cybersecurity measures implemented, and user instructions for secure installation and updates.
CE marking. The familiar CE mark will now also certify that a product meets cybersecurity requirements. Products that fail to comply lose their CE marking and their legal right to be sold in the EU.
Why This Matters Specifically for Lighting
The entertainment lighting industry has operated on unauthenticated, unencrypted protocols for decades. Art-Net sends DMX data as plaintext UDP packets with no authentication. sACN does the same. RDM has no access control. These protocols were designed for closed, trusted, physically isolated networks where security was handled by keeping the network cable away from unauthorized hands.
The CRA doesn't specifically mention Art-Net or sACN. It works at a higher level, requiring manufacturers to assess the cybersecurity risks of their products and implement "appropriate" protections.
The key question for every lighting manufacturer becomes: can you argue in your risk assessment that an unauthenticated network interface meets the CRA's "secure by default" requirement?
The answer depends heavily on the product's intended use and threat model. A fixture designed exclusively for physically isolated lighting networks has a different risk profile than a gateway that bridges lighting and IT networks. But the risk assessment must be documented, defensible, and maintained, and market surveillance authorities will be the ones judging whether a manufacturer's assessment is adequate.
This is precisely the gap that Sig-Net, the new protocol launched at PLASA PlugFest in April 2026 by Art-Net creator Wayne Howell, is designed to fill. Sig-Net provides an authentication and integrity framework specifically built for the realities of live production, giving manufacturers a concrete reference point for their CRA risk assessments without requiring full encryption of real-time DMX data.
The Penalties
The CRA includes significant enforcement mechanisms. Fines can reach up to 15 million euros or 2.5% of global annual turnover, whichever is higher. Market surveillance authorities can also withdraw non-compliant products from the EU market entirely.
For a small or mid-size lighting manufacturer, the withdrawal risk may be more immediately threatening than the fine. Losing access to the European market, even temporarily, could be existential.
What Manufacturers Should Be Doing Now
The December 2027 deadline sounds far away. It isn't. Product development cycles in the lighting industry typically run 12 to 24 months. A product entering the design phase today needs to be CRA-compliant at launch.
The immediate priorities:
- start the risk assessment process for every networked product in your portfolio,
- audit your existing products for planned firmware or software updates as any substantial modification after December 2027 triggers full CRA compliance requirements for that product, even if it was originally placed on the market years earlier.
- evaluate what security measures are proportionate to each product's threat profile,
- establish a vulnerability management process if you don't already have one, and
- begin building the technical documentation the regulation requires.
One approach some manufacturers are already exploring is replacing their existing network stack entirely rather than retrofitting security into legacy code. Licensable protocol libraries with Sig-Net support built in can significantly shorten the path to a CRA-defensible product, especially for manufacturers whose current stack was sourced from third-party OEMs without cybersecurity in mind.
QubiCast's own QubiCore library takes this approach, providing a complete lighting network stack with protocol support and security framework in a single licensable package.
The reporting obligations start in September 2026. That's five months from now. If your products have network interfaces and you're selling them in Europe, the clock is already running.
For a deeper look at how the industry is responding, including the Sig-Net protocol and its approach to CRA-defensible security, read our coverage of the PLASA PlugFest launch.